Listen to the Podcast
19 Apr 2024 - Podcast #878 - (16:46)
It's Like NPR on the Web
If you find the information TechByter Worldwide provides useful or interesting, please consider a contribution.

If you find the information TechByter Worldwide provides useful or interesting, please consider a contribution.
Microsoft will end support for Windows 10 about 18 months from now. You’ll still be able to use the computer, but the operating system will no longer receive security updates. The obvious possibilities include upgrading the computer to Windows 11, but that may not be possible. If you’ve already upgraded an “unsupported” computer to Windows 11, that upgrade may not stick. So what are the options?
Click any small image for a full-size view. To dismiss the larger image, press ESC or tap outside the image.
 Let’s start with the worst possible choice: Throw the computer into a landfill. Please! Don’t do that! At the very least, find a way to keep it out of a landfill.
Let’s start with the worst possible choice: Throw the computer into a landfill. Please! Don’t do that! At the very least, find a way to keep it out of a landfill.
Second Worst Choice: Just keep using the computer even though you will not receive any security updates. That does keep the computer out of a landfill, but it exposes you and every bit of information on your computer to unacceptable risks.
People are still using computers with Windows XP, so your Windows 10 PC won’t magically shut down, levitate away, or halt and catch fire on 14 October 2025. But the danger will increase on every day that passes. Crooks like to find security flaws in old operating systems because they know the bugs will never be squished. Antivirus vendors are likely to continue supporting Windows 10 computers for a while, but third-party protective applications can’t address operating system bugs.
There is one exception in which the danger doesn’t increase significantly: A Windows 10 computer that is not connected to the internet in any way, wired or wireless, will be relatively safe. But don’t transfer files to or from the computer with a thumb drive.
Upgrading an unsupported computer to Windows 11 is a risky approach even though it can be done. Not all of the strict requirement for Windows 11 are absolutely essential. Some of these restrictions can be ignored as I described a few weeks ago. If your Windows 10 computer isn’t fully compatible with Windows 11 but also isn’t so old that Windows 11 will not run, installing Windows 11 is possible.
The trouble is that these “unsupported” installations aren’t guaranteed to receive updates. Unless the computer is more than 10 years old, those who spend a lot of time trying to decipher Microsoft tea leaves seem to think that these middle-ground computers will probably continue to run normally and receive security updates. If you want to go this route, see Adding Windows 11 To A Reluctant Windows 10 PC from 2 Feb 2024.
 If you don’t need the computer to run Windows, you could install Google’s ChromeOS Flex or one of the Linux variants. ChromeOS Flex won’t convert the computer to be a Chromebook, but ChromeOS Flex will continue to receive security updates. ChromeOS Flex doesn’t support every PC, but unlike Windows 11, it will install on unsupported PCs. Beware, though, that not all hardware is guaranteed to work if the computer isn’t supported and ChromeOS Flex doesn’t have all the features you’ll find on a real Chromebook.
If you don’t need the computer to run Windows, you could install Google’s ChromeOS Flex or one of the Linux variants. ChromeOS Flex won’t convert the computer to be a Chromebook, but ChromeOS Flex will continue to receive security updates. ChromeOS Flex doesn’t support every PC, but unlike Windows 11, it will install on unsupported PCs. Beware, though, that not all hardware is guaranteed to work if the computer isn’t supported and ChromeOS Flex doesn’t have all the features you’ll find on a real Chromebook.
 Installing Linux on a Windows computer has some of the same drawbacks as ChromeOS Flex: Some hardware devices may not work. This is the case for hardware that uses proprietary device drivers. Linux is reliable and some distros closely mimic Windows. Even with WINE, not all Windows applications will run under Linux. Unless you’re tied to Windows apps that won’t run under Linux, this can be a very good choice.
Installing Linux on a Windows computer has some of the same drawbacks as ChromeOS Flex: Some hardware devices may not work. This is the case for hardware that uses proprietary device drivers. Linux is reliable and some distros closely mimic Windows. Even with WINE, not all Windows applications will run under Linux. Unless you’re tied to Windows apps that won’t run under Linux, this can be a very good choice.
And finally, the easiest and possibly the best solution—if you want to continue running Windows 10—is simply to pay Microsoft for the Extended Security Update Program. Microsoft has offered extended support like this to enterprise users for Windows XP and Windows 7, but has never made the offer to home and small office users.
We don’t yet know how much Microsoft will charge, but we do know that there will be no feature updates for Windows 10 after October 2025. Users who enroll in the subscription plan will receive security updates for up to three years. Business users paid $50 per computer for the first year’s extended support for Windows 7. The price increased to $100 the second year and $200 the third year.
If you simply want to continue using a Windows 10 computer until late 2026, spending $50 for one year’s worth of extended support could be a very good choice.
When I had to rename a lot of files, it occurred to me that it’s been a while since I mentioned the importance of having a comprehensive file renamer on the computer. Even if you’ve installed Microsoft’s free PowerToys and have activated the PowerRename utility, there are good reasons to obtain the equally free Bulk Rename Utility.
The PowerRename utility works well, but is somewhat limited. The Bulk Rename Utility offers an astonishingly large number of features and options, but can be intimidating. Let’s take a quick look at both.
Click any small image for a full-size view. To dismiss the larger image, press ESC or tap outside the image.
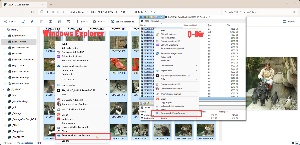 To open PowerRename after installing PowerToys and activating the function, select files in the Windows File Explorer or another file browser such as Q-Dir. Right-click the block of selected files, and choose Rename with PowerRename. You may need to select More Options from the first context menu.
To open PowerRename after installing PowerToys and activating the function, select files in the Windows File Explorer or another file browser such as Q-Dir. Right-click the block of selected files, and choose Rename with PowerRename. You may need to select More Options from the first context menu.
 The files you selected will be shown and check marks will indicate that they will be renamed. For this example, I chose to change the file extension from JPG (upper case) to jpg (lower case). The dialog box’s top field contains the text to find, the second field contains the replacement text. I selected “Case sensitive” because Windows is case insensitive by default and selected Apply.
The files you selected will be shown and check marks will indicate that they will be renamed. For this example, I chose to change the file extension from JPG (upper case) to jpg (lower case). The dialog box’s top field contains the text to find, the second field contains the replacement text. I selected “Case sensitive” because Windows is case insensitive by default and selected Apply.
Two files were not changed. One was a Photoshop file (PSD) and the other was a JPEG file that already had a lower case extension.
I could also have left the text boxes empty, told PowerRename to apply changes to the extension only, and selected the aa (lower case) text formatting button. Quick. Simple. Easy. But perhaps you need to do something more complex, and that’s what the Bulk Rename Utility can do.
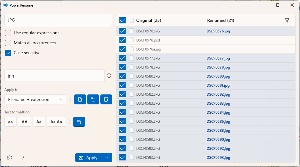
To use the Bulk Rename Utility, which is free for non-commercial use, open the app and navigate to the directory where the files are.
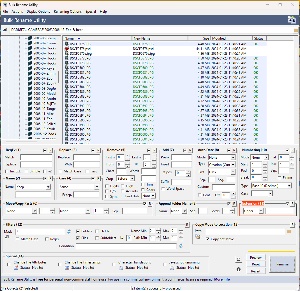 I’ll start with a simple change that reverses the change I made with PowerRename. After selecting all the files in the directory, I could choose option 11 (Extension) and specify upper case. That would change all files, including PSD files and some JPEG files that initially had lower case extensions. That’s the fastest and easiest option, but not quite what I want. So I selected only the files I wanted to modify and clicked Rename. Equally quick, simple, and easy.
I’ll start with a simple change that reverses the change I made with PowerRename. After selecting all the files in the directory, I could choose option 11 (Extension) and specify upper case. That would change all files, including PSD files and some JPEG files that initially had lower case extensions. That’s the fastest and easiest option, but not quite what I want. So I selected only the files I wanted to modify and clicked Rename. Equally quick, simple, and easy.
But what if you’ve returned from a trip to the zoo and you have more than 100 files with names like “DSCF0575.JPG”. You’d prefer the files to have names that are more descriptive. Something like “Zoo-2024-04-04” to indicate the subject and the date. That’s good, but you’ll also need a sequential number or some sort of identifier to differentiate each individual file. And maybe these are images you took and you want to be able to identify which photos are yours because your husband’s pictures will also uploaded to this directory. So maybe something like “Zoo-(bb)2024-04-04” to add your initials and “Zoo-(bb)2024-04-04-NNN” where NNN is a 3-digit number.
Some photo applications such as Adobe Lightroom can rename files as they are imported, but not all applications can do this.
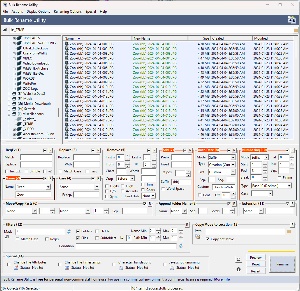 Bulk Rename Utility can handle all the changes in a single go. Start by selecting all the files. Use option 2 (Name) to specify “Zoo-”, then move to option 7 (Add) and add “(bb)-” as a suffix. Next choose option 8 (Auto Date) and specify a custom format as a suffix. Enter “%Y-%m-%d-” to produce the date as “2024-04-04” with a trailing dash. Now all that’s left is the sequential number. Move to option 10 (Numbering) and specify that the numbering should be placed as a suffix, start at 1, increment by 1, and be padded to 3 spaces. Click Rename and you’re done.
Bulk Rename Utility can handle all the changes in a single go. Start by selecting all the files. Use option 2 (Name) to specify “Zoo-”, then move to option 7 (Add) and add “(bb)-” as a suffix. Next choose option 8 (Auto Date) and specify a custom format as a suffix. Enter “%Y-%m-%d-” to produce the date as “2024-04-04” with a trailing dash. Now all that’s left is the sequential number. Move to option 10 (Numbering) and specify that the numbering should be placed as a suffix, start at 1, increment by 1, and be padded to 3 spaces. Click Rename and you’re done.
The Bulk Rename Utility, which is free for personal use, offers an amazing number of options, and that’s why some people panic when they see the interface. So the important first step is to understand that you don’t have to fill out all the little text boxes and place check marks in any of the selectors. Use only the ones you need to specify the name change you want and leave everything else alone.
There are 14 major sections that include nearly 30 text boxes, more than 20 check boxes, and about a dozen drop-down selection lists. If you want to know how every part of the program works, you can download a manual, which is more than 50 pages long. There’s also a handy online FAQ that answers a lot of questions.
You may not need any of that because it’s easy to read the section headings on the user interface and figure out which ones you need.
You may not need to rename a lot of files every day, but there’s nothing better than the Bulk Rename Utility when you do. It’s free for home and non-commercial use, but commercial users should plan to license the application. Additional details are available on the Bulk Rename Utility website.
Microsoft keyboards will soon have an artificial intelligence key, but there are other ways to get Copilot’s attention. There’s already a key for emoticons on some keyboards, but you don’t need that either, particularly if you need accented characters found in many languages.
Click any small image for a full-size view. To dismiss the larger image, press ESC or tap outside the image.
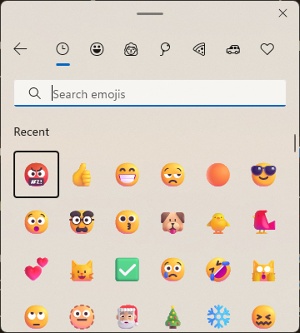 Keyboards with the special emoticon key make it easy to open the panel with emojis, GIFs, antique ASCII emoticons, some special characters, and the Windows clipboard. But how much harder is it to press the Windows key and a period? You’ll get the same result.
Keyboards with the special emoticon key make it easy to open the panel with emojis, GIFs, antique ASCII emoticons, some special characters, and the Windows clipboard. But how much harder is it to press the Windows key and a period? You’ll get the same result.
Microsoft’s emoticon selector doesn’t make it easy to insert typographic characters, though, because you’ll have to scroll through a long list. The ones you use most often will be collected automatically at the top of the list. The numeric keypad sequences needed for special characters that people use frequently are fairly easy to memorize: Bullet points (• Alt-0149), e acute (é Alt-0233), fractions (¼ Alt-0188, ½ Alt-0189, ¾ Alt-0190), or the cent symbol (¢ Alt-0162). But what about the ones you don’t use very often? The Euro (€), copyright and trademark symbols (©, ™, ®), and such? You may have a printed chart nearby or you might visit a website or just use a Google search to find the code. Wouldn’t it be nice if you could just click a couple of keys and then pick what you need?
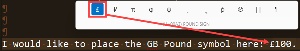 In fact, you can do that if you’ve installed PowerToys Quick Accent. Define how to activate the utility and hundreds of special characters are at your call. Need a lower case O with an umlaut. Easy! Press and hold the O key, then immediately press the activation key. While continuing to hold the O key, press the left or right arrow key to select ö (lower case O with an umlaut) and release the key.
In fact, you can do that if you’ve installed PowerToys Quick Accent. Define how to activate the utility and hundreds of special characters are at your call. Need a lower case O with an umlaut. Easy! Press and hold the O key, then immediately press the activation key. While continuing to hold the O key, press the left or right arrow key to select ö (lower case O with an umlaut) and release the key.
Need a Euro symbol? Euro starts with E so start there and you’ll soon have a € symbol. Yen begins with a Y, so start with Y to get the ¥ symbol. Pound? Yeah, you’re ahead of me. Start with the P key to get the £.
The activation key can be the spacebar or the left and right arrow keys, or any of those options.